Ever reset a password and forget it in the next five minutes? Happens more than we admit.
Ten apps, ten passwords, and one sleepy brain before your first sip of coffee. Sounds funny, but it’s a real problem. People reuse passwords, write them on sticky notes, or pick the easiest option. That’s not just messy, it’s risky.
This is where Security Assertion Markup Language quietly changes the game. It removes the chaos of multiple logins and replaces it with one smooth entry point.
No juggling. No confusion. Just access. But here’s the real question: how does one login unlock so many doors without compromising security? And why do big companies rely on it every day?
Let’s simplify it.
What is Security Assertion Markup Language (SAML)? Key Components of SAML

Security Assertion Markup Language (SAML) is an open standard that allows systems to share authentication and authorization data in a secure way. In simple words, it acts like a trusted pass that proves your identity across different platforms.
Instead of logging in again and again, SAML sends a secure digital message that confirms you are already verified. This reduces password usage and lowers the risk of security breaches.
Think of it like showing your ID once at the entrance of a building and then moving freely inside without repeated checks. That is how SAML simplifies access while keeping everything secure.
Key Components of SAML
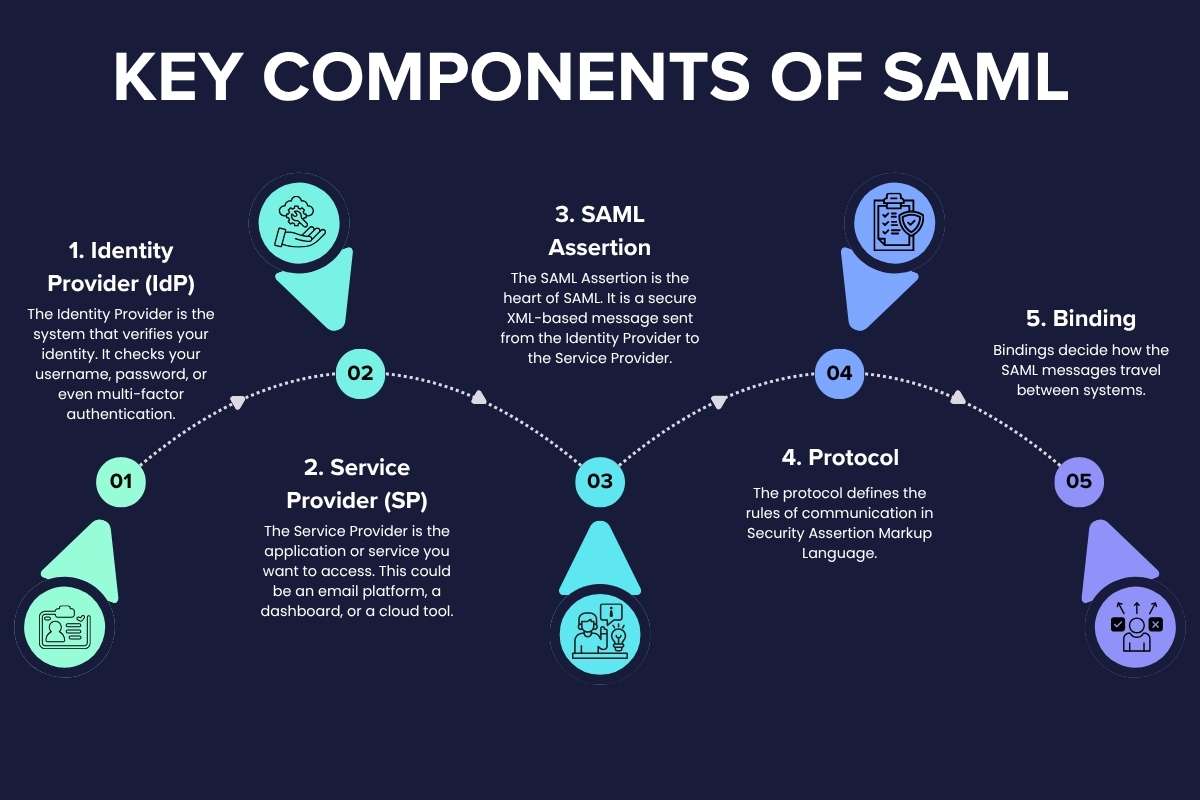
Each part of the Security Assertion Markup Language plays a specific role. Together, they create a smooth and secure login experience.
1. Identity Provider (IdP)
The Identity Provider is the system that verifies your identity. It checks your username, password, or even multi-factor authentication.
Once verified, the Identity Provider confirms that you are a valid user. In a SAML setup, this is the most trusted authority.
Examples include company login systems or authentication platforms like corporate directories.
2. Service Provider (SP)
The Service Provider is the application or service you want to access. This could be an email platform, a dashboard, or a cloud tool.
Instead of asking for login details, the Service Provider trusts the Identity Provider. With Security Assertion Markup Language, it accepts the authentication proof and grants access.
This trust relationship is what makes the process seamless.
3. SAML Assertion
The SAML Assertion is the heart of SAML. It is a secure XML-based message sent from the Identity Provider to the Service Provider.
It contains important details such as:
- Who the user is
- When the user logged in
- What permissions the user has
This assertion acts like a digital certificate. It proves that authentication has already happened.
4. Protocol
The protocol defines the rules of communication in Security Assertion Markup Language.
It explains how requests are made and how responses are sent. It ensures that both systems understand each other clearly.
Without this structure, the exchange of authentication data would be messy and unreliable.
5. Binding
Bindings decide how the SAML messages travel between systems.
Common methods include:
- HTTP Redirect
- HTTP POST
It ensures that data moves securely through browsers or networks without being exposed.
Each component works together to make Security Assertion Markup Language fast, secure, and reliable.
Also Read: The Importance of Multi-Factor Authentication: Protecting What Matters Most
Why SAML is Important in Modern Digital Security? Benefits of Using SAML

Modern workplaces run on multiple apps. Teams switch between email, dashboards, cloud tools, and internal systems all day. Without SAML, users would need a different password for each platform. That leads to confusion, weak password habits, and a higher risk.
People often reuse passwords or write them down. Both actions create easy entry points for attackers. This is where Security Assertion Markup Language changes the game. It creates a secure bridge between systems so users don’t have to prove their identity again and again.
Why It Matters?
SAML reduces password exposure at its core. When users log in once through a trusted Identity Provider, they don’t need to share credentials with every app. This cuts down the chances of password theft.
It also brings control to one place. Instead of managing access across many systems, teams handle everything centrally. With Security Assertion Markup Language, admins can track who logs in, when they log in, and what they can access.
This level of visibility helps detect unusual behavior quickly. If something feels off, action can be taken right away. That makes SAMLa a strong layer in modern security strategy.
Another key point is trust. Systems trust the Identity Provider. This removes repeated verification steps and creates a smooth, secure flow. SAML builds that trust between platforms without exposing sensitive data.
Benefits

1. Better Security
Security Assertion Markup Language removes the need to store passwords across multiple systems. Fewer storage points mean fewer attack surfaces. Hackers have fewer doors to knock on.
It also supports strong authentication methods. When combined with multi-factor authentication, SAML adds an extra shield to user accounts.
2. Improved User Experience
No one enjoys repeated logins. With SAML, users sign in once and move across apps without interruption.
This creates a smooth workflow. It reduces frustration and keeps users focused. A simple login experience often leads to better productivity.
3. Faster Access
Time matters in any organization. Logging in multiple times wastes minutes that add up over the day.
SAML speeds up access. Users get instant entry to the tools they need. This helps teams work faster and stay efficient.
4. Easy Management
Managing access for hundreds or thousands of users can feel overwhelming. SAML simplifies this process.
Admins control permissions from a central system. They can grant or revoke access in seconds. This reduces manual work and lowers the chance of errors.
5. Scalability
As companies grow, their systems grow too. New tools, new users, and new access needs come into play.
Security Assertion Markup Language handles this growth with ease. It works well for small teams and scales smoothly for large enterprises. There is no need to rebuild the system as the organization expands.
Also Read: SAML vs OAuth: What’s the Difference and Which One Do You Need?
How SAML Works? (Step-by-Step Flow)
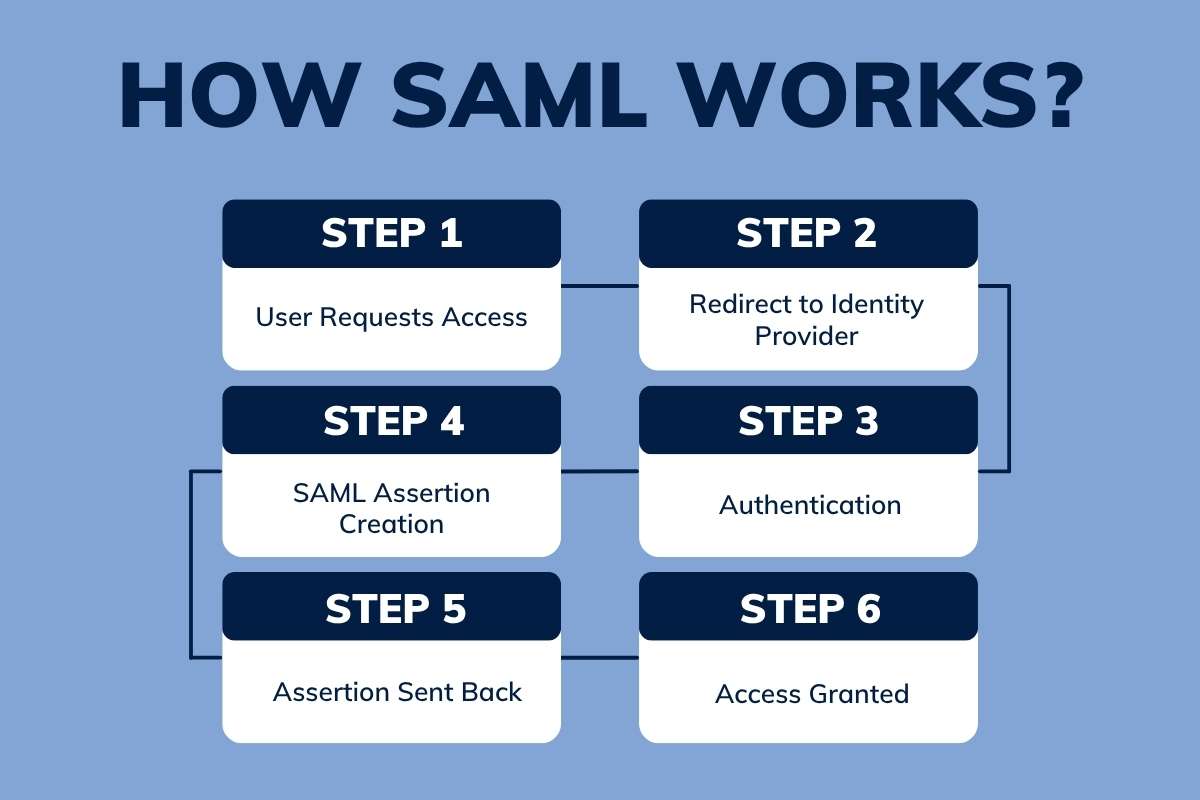
Understanding the flow of SAML is easier than it sounds.
- Step 1: User Requests Access – A user tries to open an app.
- Step 2: Redirect to Identity Provider – The app sends the user to the Identity Provider for login.
- Step 3: Authentication – The Identity Provider checks the user’s credentials.
- Step 4: SAML Assertion Creation – After verification, it creates a secure assertion using SAML.
- Step 5: Assertion Sent Back – The assertion is sent to the Service Provider.
- Step 6: Access Granted – The app trusts the assertion and allows access.
This entire process takes seconds. Security Assertion Markup Language works quietly in the background.
Explain SAML and Single Sign-On?
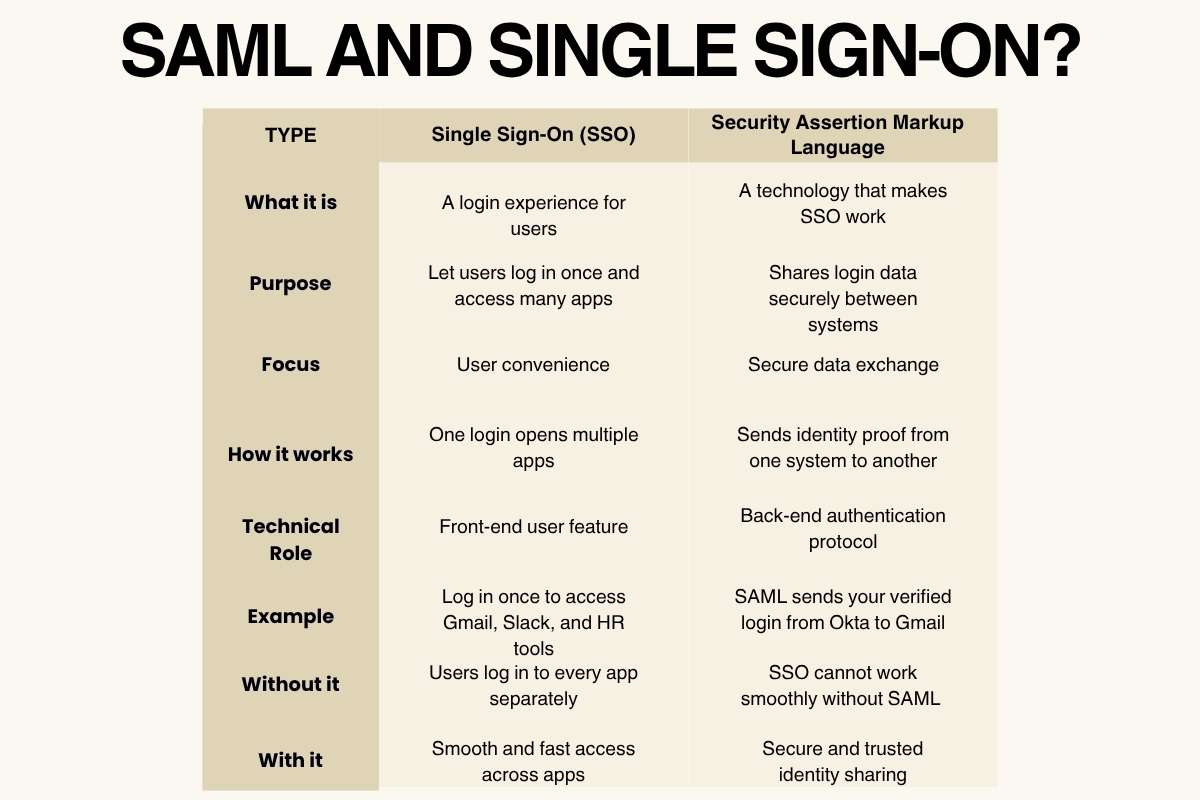
Single Sign-On (SSO) allows users to log in once and access multiple apps. SAML is one of the main technologies that powers SSO.
| Type | Single Sign-On (SSO) | Security Assertion Markup Language |
| What it is | A login experience for users | A technology that makes SSO work |
| Purpose | Let users log in once and access many apps | Shares login data securely between systems |
| Focus | User convenience | Secure data exchange |
| How it works | One login opens multiple apps | Sends identity proof from one system to another |
| Technical Role | Front-end user feature | Back-end authentication protocol |
| Example | Log in once to access Gmail, Slack, and HR tools | SAML sends your verified login from Okta to Gmail |
| Without it | Users log in to every app separately | SSO cannot work smoothly without SAML |
| With it | Smooth and fast access across apps | Secure and trusted identity sharing |
Challenges and Limitations of SAML
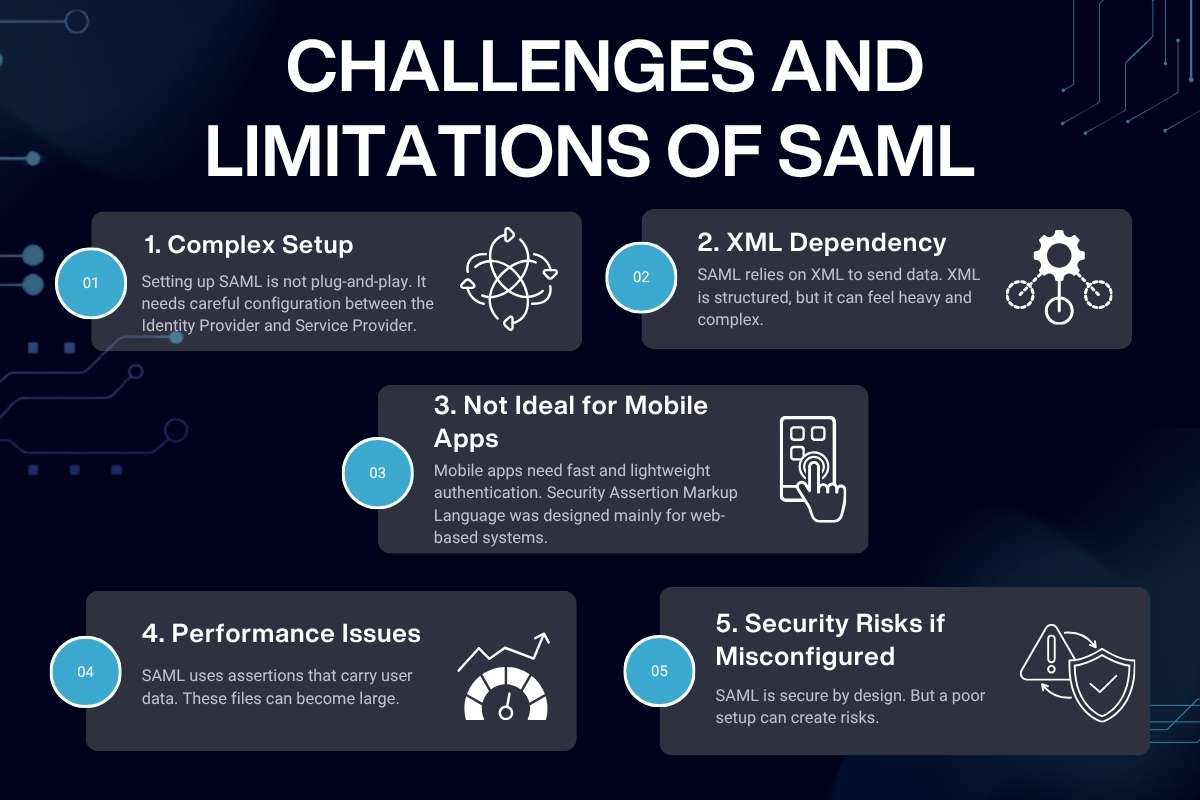
Even though Security Assertion Markup Language is powerful, it comes with a few real-world challenges. These do not make it weak, but they do require attention during setup and use.
1. Complex Setup
Setting up SAML is not plug-and-play. It needs careful configuration between the Identity Provider and Service Provider.
Each system must trust the other. Certificates, endpoints, and metadata must match correctly. A small mistake can break the login flow.
Teams often need skilled developers or IT experts to handle SAML integration. This makes the initial setup slow for some organizations.
2. XML Dependency
SAML relies on XML to send data. XML is structured, but it can feel heavy and complex.
Debugging XML files takes time. Even a small error in tags or formatting can stop the process.
Modern developers often prefer lighter formats like JSON. Compared to them, XML used in SAML feels outdated and harder to manage.
3. Not Ideal for Mobile Apps
Mobile apps need fast and lightweight authentication. Security Assertion Markup Language was designed mainly for web-based systems.
It does not fit smoothly into mobile-first environments. Developers often need extra layers or workarounds.
Because of this, many mobile apps choose newer methods instead of SAML.
4. Performance Issues
SAML uses assertions that carry user data. These files can become large.
Large assertions take more time to process and transfer. This can slow down login speed, especially in high-traffic systems.
In most cases, the delay is small. But at scale, it can affect performance if Security Assertion Markup Language is not optimized properly.
5. Security Risks if Misconfigured
SAML is secure by design. But a poor setup can create risks.
If certificates are not managed well, attackers may exploit the system. If validation rules are weak, fake assertions might pass through.
This is why proper configuration and regular checks are critical when using SAML.
Despite these challenges, many organizations still rely on SAML. Its strong structure, proven reliability, and wide adoption make it a trusted choice.
Future of SAML in Identity Management
The future of SAML looks stable, even as technology evolves. It may not be the newest option, but it still plays a key role in identity systems.
New protocols like OAuth and OpenID Connect are growing fast. They offer flexibility and better support for modern apps. Still, Security Assertion Markup Language remains strong in enterprise environments where stability matters most.
What Lies Ahead
1. Hybrid Systems
Many companies now use a mix of technologies. They combine SAML with newer protocols.
This approach gives them the best of both worlds. They keep existing systems running while adding modern features.
2. Continued Enterprise Use
Large organizations trust SAML for internal systems. It handles complex environments with many users and services.
Its reliability keeps it relevant, especially in industries that value stability over change.
3. Improved Integration
Integration tools are getting better. Developers now have simpler ways to connect apps using Security Assertion Markup Language.
Pre-built solutions and cloud services reduce setup time. This makes adoption easier than before.
4. Better Security Layers
Security continues to improve around SAML. Multi-factor authentication adds an extra layer of protection.
Even if one step fails, additional checks keep systems safe. This strengthens trust in SAML systems.
Conclusion
Remember that daily password struggle? Now imagine a smooth login that just works. That’s the quiet power of Security Assertion Markup Language.
It reduces friction, improves safety, and keeps systems connected without chaos. While newer tools enter the space, this standard still stands strong in many organizations.
It proves that simple ideas, when built well, last long. In a world full of logins, SAML keeps things calm, secure, and efficient, just the way users like it.
FAQs
1. What is Security Assertion Markup Language in simple terms?
A: It is a standard that allows systems to share login information securely so users don’t need multiple passwords.
2. Is SAML still used today?
A: Yes, many enterprises still rely on it for secure access and identity management.
3. How is SAML different from OAuth?
A: Security Assertion Markup Language focuses on authentication, while OAuth handles authorization.
4. Is SAML secure?
A: Yes, when configured properly, SAML provides strong security.
5. Can SAML work with cloud apps?
A: Yes, many cloud services support SAML for secure access.






