Traditional cybersecurity followed a simple rule: trust users and devices inside the company network and block threats from outside.
Today, that approach is no longer enough. Employees work from ho…
- Cyber
- Cyber Attacks & Defence
Ever reset a password and forget it in the next five minutes? Happens more than we admit.
T…
Cybersecurity is growing fast, and by 2026, the U.S. will need 1.5 million more professionals in the…
Slow internet, dropped calls, and apps not loading are common problems. They interrupt work and crea…
Right now, your business is running on phones. Your sales team checks CRM on the go. Your finance te…
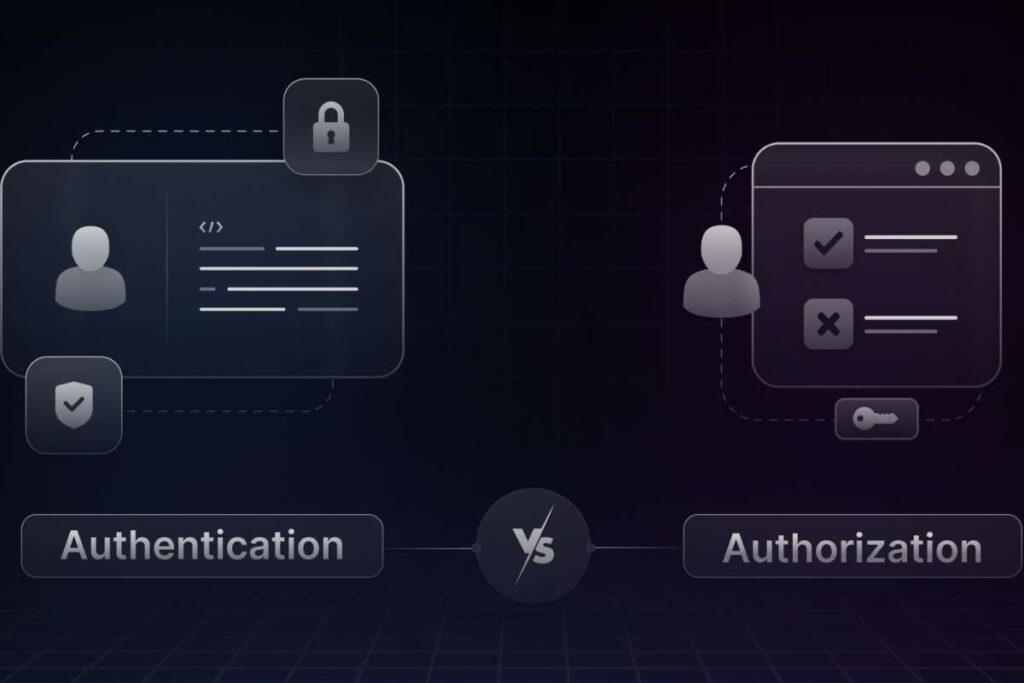
Passwords open doors. Permissions decide where you can walk.
Most people mix them up. Even tech w…
Most Popular
Most Popular
- AI & Machine Learning
- IoT
- Cloud
Building software without the right tools can waste time and increase errors. A software development toolkit gives developers the tools they need to write, test, and maintain code efficiently. It comb…
- Cyber Frauds
Phishing accounts for over 90% of cyberattacks, primarily through deceptive emails. One click can le…
Why a Threat Intelligence Platform is Now a Boardroom Imperative? Here’s Everything You Need to Know
Staying safe in the digital space is no less than a sport. Every day, you feel the quiet pressure of…
- Social Media
- Latest Updates
Key Takeaways:
Anthropic engineers are working with the NSA to deploy Mythos software.
The c…
Key Takeaways:
Meta hid dormant Facial Recognition Code within its smart glasses app.
The com…
Key Takeaways:
Researchers created a zero-click AI Worm that steals sensitive corporate data.
…
Key Takeaways:
Microsoft introduced a Microsoft wearable AI badge prototype for office employee…
Key Takeaways:
Anthropic Claude outage caused a major global outage due to capacity constraints.…
Key Takeaways:
Hackers exploited a Meta AI Security Flaw in the support chatbot to bypass secur…
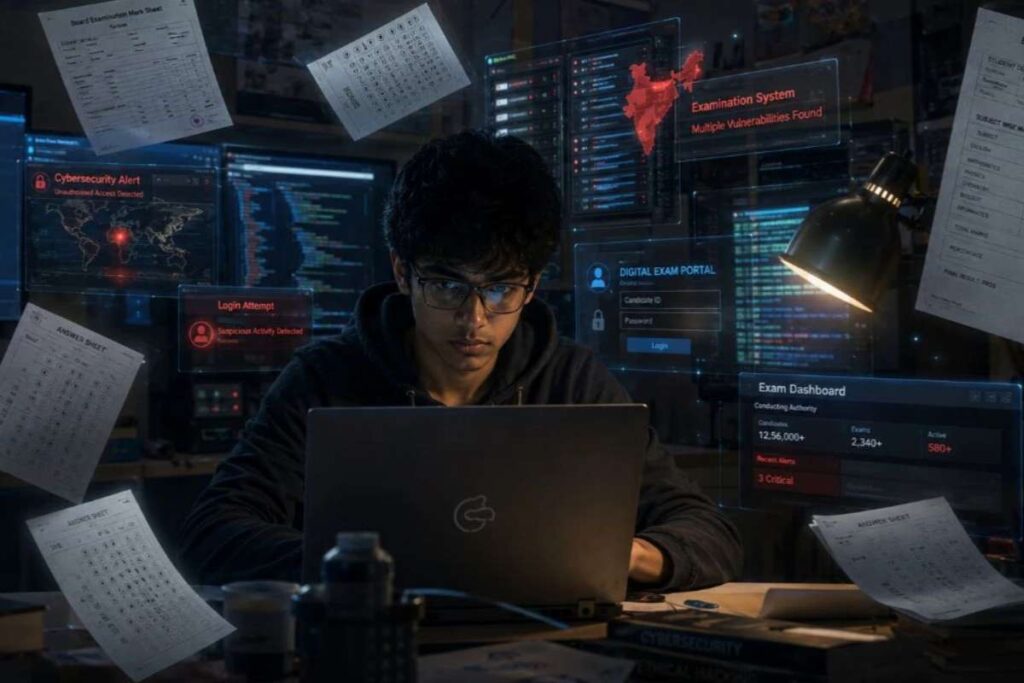
Key Takeaways
CBSE cybersecurity flaws were identified and contain vulnerabilities in the digita…
Key Takeaways
$500 million investment targets proprietary AI infrastructure and data control.
…