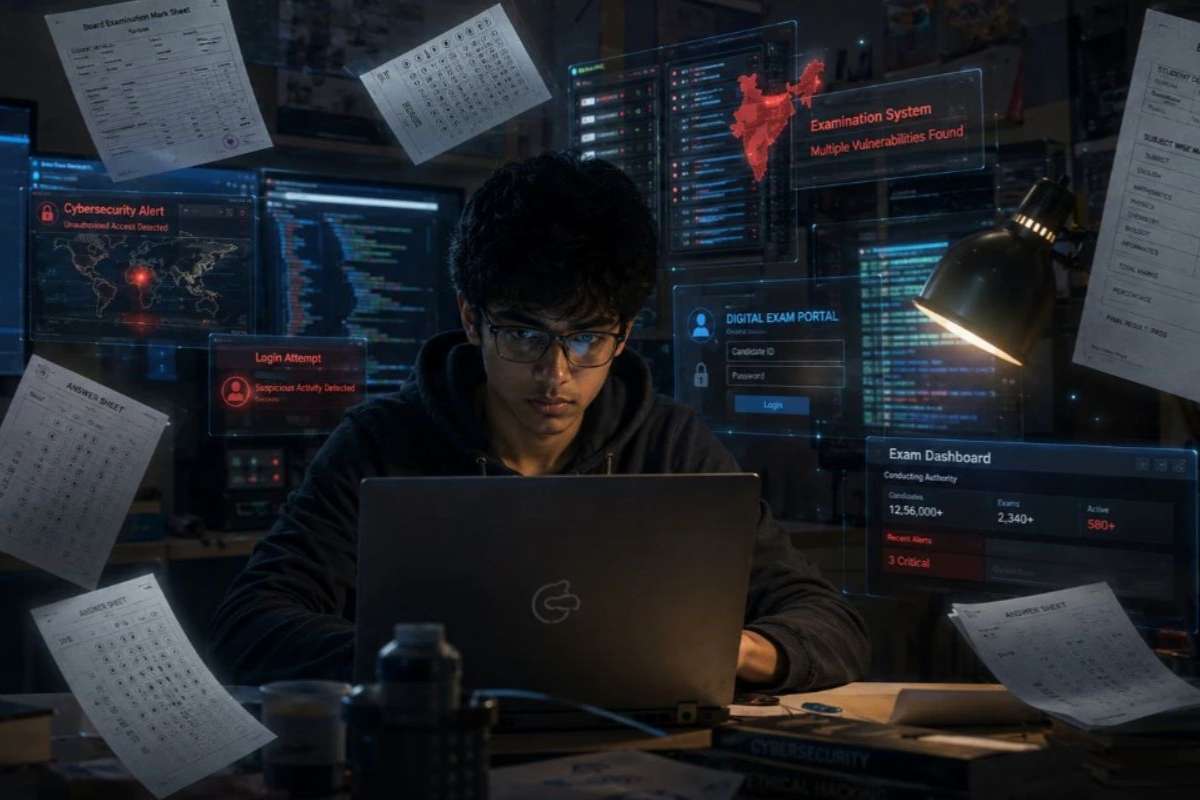
The impact of cyber-attacks on businesses can be massive. In the interconnected realm of the digital age, cyber-attacks on businesses have become a prevalent and ever-evolving threat. As organizations increasingly rely on technology for their daily operations, the vulnerabilities to cyber threats multiply. This article delves into the profound impact that cyber-attacks can have on businesses and underscores the critical importance of implementing robust cyber security measures to fortify against these insidious threats.
The Rising Tide of Cyber Attacks on Businesses:
In recent years, the frequency and sophistication of cyber attacks on businesses have reached alarming levels. From multinational corporations to small enterprises, no entity is immune to the far-reaching consequences of these digital assaults. Cyber attackers, driven by diverse motives ranging from financial gain to political espionage, exploit vulnerabilities in network systems, software, and human behavior to breach organizational defenses.
The Financial Toll of Cyber-Attacks:
The financial implications of cyber-attacks on businesses are staggering. Incidents such as data breaches, ransomware attacks, and financial fraud can result in direct monetary losses, regulatory fines, and legal expenses. The aftermath of a cyber-attack often includes the cost of investigating the breach, restoring compromised systems, and compensating affected customers or clients. The financial repercussions extend far beyond the immediate aftermath, with long-term damage to the organization’s reputation and trust among stakeholders.
Reputational Damage and Loss of Customer Trust:
One of the most significant impacts of cyber-attacks on businesses is the erosion of trust. When customer data is compromised, the reputational fallout can be severe. The loss of trust among customers and clients may lead to a decline in brand loyalty and, in extreme cases, result in customers seeking alternative, more secure options. Rebuilding trust post-cyber-attacks is a formidable challenge, requiring not only financial investment but also transparent communication and a commitment to enhanced cyber security.
Operational Disruptions and Downtime:

Cyber-attacks have the potential to paralyze business operations. Ransomware attacks, for instance, can encrypt critical files and demand a ransom for their release. The downtime caused by such incidents translates into lost productivity, missed deadlines, and disrupted supply chain activities. In industries where time-sensitive operations are crucial, such as manufacturing and healthcare, the impact of cyber-attacks on businesses can be particularly detrimental.
Intellectual Property Theft and Corporate Espionage:
Beyond financial gains, cyber attackers often target businesses to steal intellectual property and proprietary information. In sectors driven by innovation, such as technology and pharmaceuticals, the loss of valuable intellectual property can cripple a company’s competitive edge. Corporate espionage through cyber means has become a significant concern, underscoring the importance of safeguarding sensitive business information.
The Human Factor: Employee Productivity and Morale:
The impact of cyber-attacks extends beyond the tangible consequences, affecting the human element within organizations. Employees, tasked with mitigating the fallout of a cyber-attack, may experience heightened stress and anxiety. Productivity can decline as teams divert their attention from regular tasks to address cyber security issues. Moreover, the morale of employees may suffer in the aftermath of a breach, affecting the overall workplace atmosphere.
Importance of Robust Cyber Security Measures:

Given the multifaceted impact of cyber-attacks on businesses, the imperative for robust cyber security measures cannot be overstated. Proactive cyber security strategies serve as a formidable defense against evolving threats and mitigate the potential fallout of cyber-attacks. Here are key considerations for organizations aiming to fortify their cyber defenses:
1. Comprehensive Risk Assessment:
Undertake a thorough risk assessment to identify and understand potential vulnerabilities within the organization’s infrastructure. Assessing risks enables businesses to prioritize cybersecurity efforts and allocate resources effectively.
2. Regular Software Updates and Patch Management:
Ensure that all software, including operating systems and applications, is regularly updated with the latest security patches. Cyber attackers often exploit outdated software to gain unauthorized access to systems.
3. Employee Training and Awareness Programs:
Human error remains a significant contributor to cyber vulnerabilities. Implement ongoing training programs to educate employees on cybersecurity best practices, recognizing phishing attempts, and maintaining strong password hygiene.
4. Network Security Measures:
Implement robust network security measures, including firewalls, intrusion detection systems, and secure Wi-Fi protocols. Securing the network perimeter is crucial in preventing unauthorized access and data breaches.
5. Data Encryption and Access Controls:
Encrypt sensitive data both in transit and at rest. Implement access controls to ensure that only authorized personnel can access critical systems and information.
6. Incident Response and Business Continuity Planning:
Develop and regularly update incident response plans to ensure a swift and coordinated response in the event of a cyber-attack. Business continuity planning is essential to minimize downtime and operational disruptions.
7. Endpoint Security:
Strengthen endpoint security by deploying antivirus software, endpoint detection and response (EDR) solutions, and implementing mobile device management (MDM) policies for devices used within the organization.
8. Collaboration with Cyber Security Experts:

Collaborate with cyber security experts and consultants to stay abreast of the latest threats and trends. Engaging external expertise can provide valuable insights and recommendations for enhancing cyber security posture.
9. Regulatory Compliance:
Ensure compliance with relevant cyber security regulations and standards. Adhering to established frameworks not only enhances cyber security practices but also helps in building a resilient defense against cyber threats.
10. Continuous Monitoring and Threat Intelligence:
Implement continuous monitoring mechanisms to detect and respond to potential threats in real-time. Incorporate threat intelligence feeds to stay informed about emerging cyber threats and vulnerabilities.
Conclusion:
The impact of cyber-attacks on businesses is far-reaching and multifaceted, encompassing financial losses, reputational damage, and operational disruptions. The imperative for robust cyber security measures cannot be overstated. As organizations navigate the digital landscape, prioritizing cyber security becomes a strategic imperative to fortify against evolving threats. The implementation of comprehensive cyber security measures not only safeguards sensitive information but also instills trust among stakeholders and ensures the resilience of businesses in the face of the persistent and evolving threat landscape posed by cyber-attacks on businesses.
Also Read: The Transformative Role of Artificial Intelligence in Cybersecurity