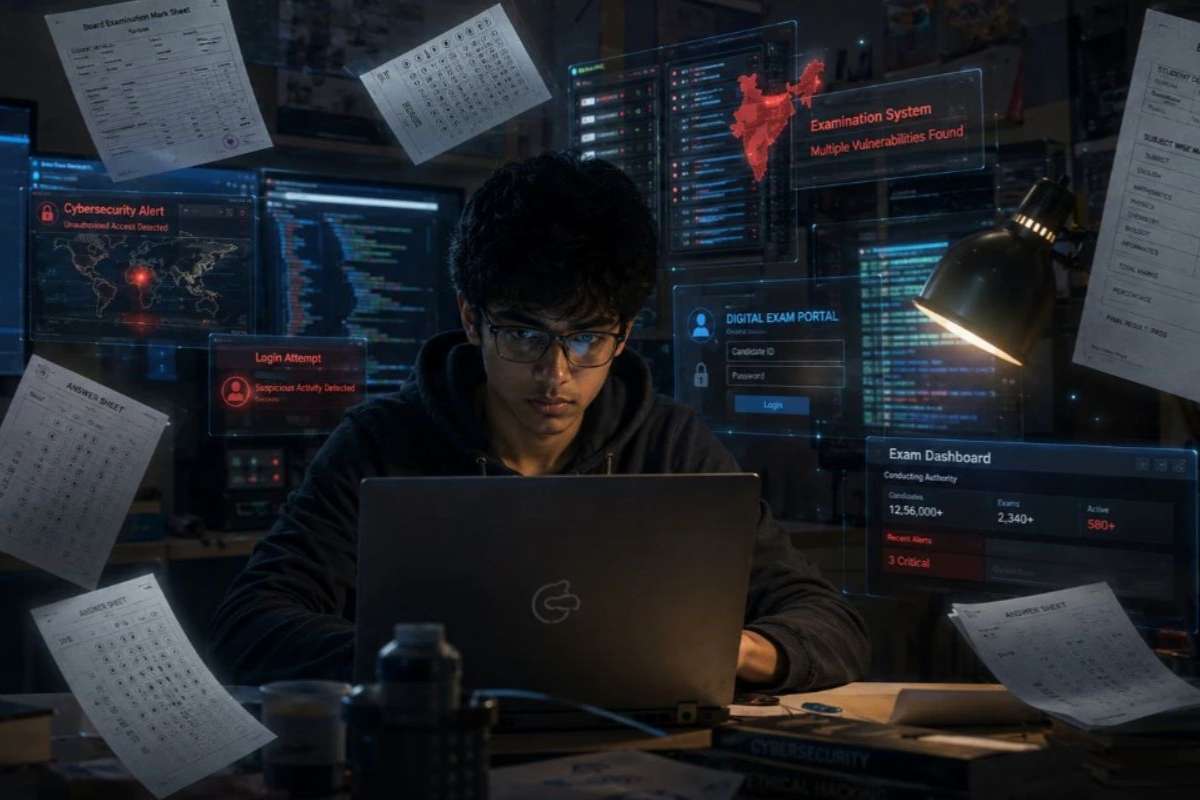
Step into the hidden corridors of the internet, where anonymity reigns supreme, and transactions occur beyond the prying eyes of search engines. This realm, known as the Dark Web (also known as the darknet), operates as a mysterious underbelly, hosting a clandestine marketplace for illicit activities. In this exploration, we unravel the enigma of the darknet, peeling back the layers that conceal its operations. From the sale of stolen data to the deployment of ransomware, it plays a pivotal role in fueling cyber threats globally.
As law enforcement grapples with the challenges posed by encrypted communications and jurisdictional complexities, the Darknet Chronicles aim to illuminate this shadowy landscape. Join us as we navigate the intricacies of the Dark Web, understanding its role in cybercrime and the ongoing efforts to combat its influence.
A Cloak of Anonymity:
The Dark Web, a subset of the deep web, requires specific software, configurations, and authorization for access. It operates on encrypted networks, most notably through Tor (The Onion Router), providing users with anonymity and obfuscating the digital trails that conventional internet activities leave behind.
Marketplaces of Illicit Goods and Services:

At the heart of the darknet lies a thriving marketplace where illicit goods and services change hands. Cryptocurrencies, primarily Bitcoin, form the preferred mode of transaction, ensuring a level of anonymity for both buyers and sellers. Everything from drugs, hacking tools, stolen data, and counterfeit passports is available for purchase, creating a lucrative underground economy.
Hacking as a Service (HaaS):
The Dark Web serves as a breeding ground for cybercriminals offering their services to the highest bidder. Hacking as a Service (HaaS) platforms provide malicious actors with ready-made tools and expertise, democratizing cyber threats and enabling even those with limited technical know-how to engage in criminal activities.
Facilitating Cybercrime:
1. Stolen Data and Identity Theft:
One of the primary functions of the darknet is the sale of stolen data. Hacked credentials, personal information, and even entire identities are traded in bulk, contributing to a surge in identity theft cases. This illicit trade ecosystem not only compromises individual privacy but also poses a significant threat to businesses and organizations.
2. Ransomware-as-a-Service (RaaS):
The rise of Ransomware-as-a-Service on the Dark Web has democratized the deployment of ransomware attacks. Criminals with minimal technical skills can lease ransomware tools, launching campaigns that encrypt victims’ data and demand ransom payments in cryptocurrencies, further fueling the underground economy.
3. Illicit Trade and Contraband:
Beyond the digital realm, the darknet facilitates the trade of physical contraband. Drugs, firearms, and other illegal commodities find a marketplace where transactions occur beyond the purview of traditional law enforcement.
Law Enforcement in the Shadows: Challenges and Efforts:

1. The Encryption Conundrum:
One of the paramount challenges faced by law enforcement agencies is the encryption that shrouds Dark Web activities. The use of sophisticated cryptographic techniques renders communication and transactions virtually impenetrable, hindering investigators’ ability to track and trace criminal operations.
2. Global Jurisdictional Complexities:
It operates on a global scale, transcending geographical boundaries. Law enforcement efforts are often impeded by jurisdictional complexities, as criminal activities orchestrated on the darknet may involve actors and victims from different countries.
3. Cat-and-Mouse Game:
As law enforcement agencies develop strategies to combat darknet activities, cybercriminals respond with countermeasures, creating a perpetual cat-and-mouse game. The agility and adaptability of Dark-web actors pose continuous challenges to those tasked with maintaining cyber law and order.
Prevention and Education: Navigating the Shadows Safely:
1. Understanding the Darknet:
Education emerges as a powerful tool in the fight against cyber threats originating from the darknet. Individuals and organizations must understand the workings of this clandestine realm, recognizing the potential risks it poses to digital security.
2. Security Hygiene:
Practicing robust security hygiene is crucial in preventing cyber threats associated with the Dark Web. This includes regular software updates, strong and unique passwords, and the implementation of multifactor authentication to fortify digital defenses.
3. Vigilance and Awareness:
Staying vigilant and informed about emerging cyber threats is essential. Regularly monitoring one’s digital presence, being cautious about sharing sensitive information online, and recognizing potential phishing attempts contribute to a proactive defense against darknet-related threats.
4. Collaborative Efforts:
Collaboration at local, national, and international levels is imperative to counter the cross-border nature of darknet activities. Governments, law enforcement agencies, cybersecurity professionals, and private entities must collaborate to share intelligence and develop effective strategies.
Conclusion: Dark Web Chronicles

The Dark Web remains an enigmatic realm where anonymity collides with criminal intent. Its role in fostering cyber threats underscores the need for collaborative, international efforts to dismantle its infrastructure. As technology evolves, so too must the strategies employed by those dedicated to safeguarding the digital landscape.
In the face of the darknet’s pervasive influence, education, awareness, and technological innovation emerge as potent tools. Empowering individuals and organizations with the knowledge to fortify their digital defenses is crucial. Furthermore, international cooperation among law enforcement agencies becomes imperative to combat the borderless nature of darknet activities.
Its Chronicles serve as a reminder that the fight against cyber threats extends beyond the visible surface of the internet. By shedding light on the clandestine operations within the Dark Web, we take a step toward demystifying the shadows and fortifying our collective resilience against the ever-evolving landscape of cybercrime.