Every 39 seconds, a cyberattack hits somewhere in the world. In the United States, the stakes have never been higher. In this high-risk environment, cybersecurity incident response is no longer just an IT function. It is a business-critical capability.
Businesses of all sizes face constant cyber threats, and the cost of doing nothing can be surprisingly high. In the U.S., the average cost of a data breach has crossed $10 million in recent years.
Attackers are faster, smarter, and more persistent than ever. They often remain undetected inside networks for months. The difference between a temporary disruption and a company-defining crisis often comes down to one factor. That is, how well your incident response plan performs under pressure.
What is Cybersecurity Incident Response?

Incident response is a structured process. It is a plan to detect, contain, eliminate, and recover from security incidents. It focuses on:
- Reducing operational downtime
- Limiting financial losses
- Protecting sensitive data
- Preserving regulatory compliance
- Safeguarding brand reputation
A mature response program ensures that when something goes wrong, the organization responds with coordination instead of chaos.
The Most Common Cybersecurity Incidents You Must Be Ready For

To build an effective cybersecurity incident response plan, you need to understand the types of threats your organization may face. Below is a breakdown of the most common security incidents mentioned above:
1. Ransomware Attacks
Ransomware is malicious software that encrypts your files or systems and demands payment for their release. These attacks can stop operations, lock employees out of critical systems, and cause significant financial damage. Modern ransomware groups often steal data before encryption, increasing pressure by threatening public exposure.
2. Insider Threats
Insider threats originate from within the organization. This may involve employees, contractors, or partners who intentionally or accidentally compromise security. Examples include data theft, misuse of access privileges, or falling victim to phishing schemes. Because insiders already have authorized access, these incidents can be difficult to detect.
3. Business Email Compromise (BEC)
BEC attacks involve cybercriminals impersonating executives, vendors, or trusted partners through email. Their goal is usually financial fraud, such as tricking employees into transferring funds or sharing sensitive information. These attacks rely heavily on social engineering rather than malware. It makes the awareness and verification processes critical.
4. Supply Chain Attacks
Supply chain attacks target third-party vendors or service providers to gain access to a primary organization. Instead of attacking you directly, criminals exploit vulnerabilities in trusted partners, software updates, or service integrations. These attacks can spread quickly and affect multiple organizations simultaneously.
Why Effective Cybersecurity Incident Response is Critical for Your Business?

Cyber incidents affect far more than just IT systems. They can disrupt revenue continuity, erode customer trust, shake shareholder confidence, and create challenges for regulatory compliance. Responding quickly helps limit the costs of fixing the damage. At the same time, delays increase the risk of long-term legal and financial consequences.
For executives, cybersecurity incident response is not merely a technical responsibility. But it is a critical part of enterprise risk management.
Strong incident response improves key security metrics:
- Mean Time to Detect (MTTD): How quickly you identify threats
- Mean Time to Respond (MTTR): How fast you contain them
- Overall breach impact: Financial, operational, and reputational damage
The Cybersecurity Incident Response Lifecycle: What Happens When an Attack Occurs?

When an attack occurs, most high-performing organizations follow this structured lifecycle.
- Preparation: This comes first. You set up playbooks, assign roles, deploy monitoring tools, and run simulations. The better prepared you are, the less chaos you’ll face when things go wrong.
- Identification: This phase begins when teams detect suspicious activity. Analysts dig in, validate alerts, and figure out if you’re really under attack. Catching it early can make all the difference.
- Containment: This step focuses on limiting damage. That means isolating systems, revoking credentials, or segmenting networks to keep the damage under control.
- Eradication: Now comes the cleanup. Teams remove malware. They patched the exploited vulnerabilities. They eliminate persistence mechanisms.
- Recovery: Systems go back online safely, often from clean backups, while the team keeps an eye out for anything suspicious. It’s about getting back to normal without inviting the attackers back in.
- Lessons Learned: Teams evaluate detection gaps, response delays, and process weaknesses. They update playbooks and strengthen controls to prevent recurrence. This phase turns incidents into improvement.
How to Master the Cybersecurity Incident Response Plan?
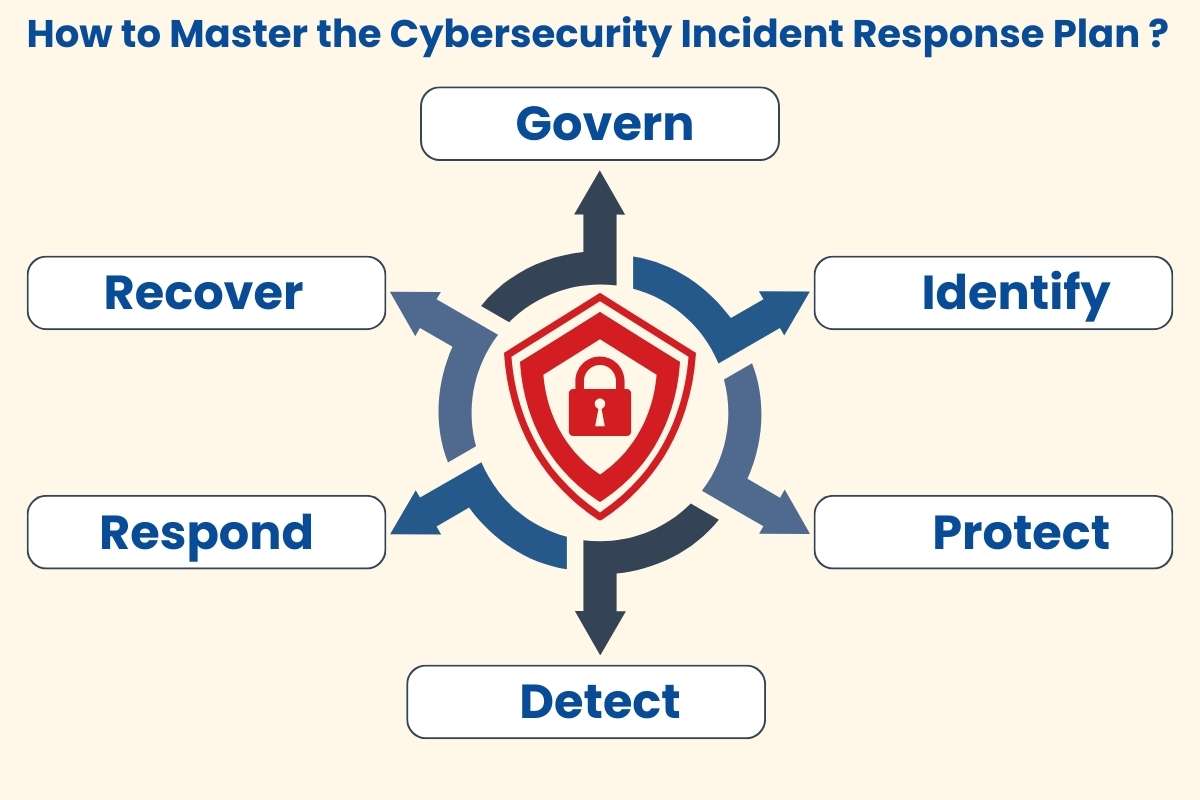
The National Institute of Standards and Technology (NIST) defines six key phases in an incident response plan:
1. Govern
Governance is the foundation. Before a breach happens, your organization must define policies, assign roles, and establish accountability. This phase ensures that incident response is not just IT’s responsibility; it’s a company-wide mandate.
Key activities include:
- Developing an incident response policy aligned with business objectives.
- Assigning ownership for incident detection, investigation, and escalation.
- Building cross-functional teams involving IT, security, legal, compliance, and PR.
- Setting clear communication protocols for internal and external stakeholders.
- Conducting tabletop exercises and simulations to test readiness.
2. Identify
Identification is about spotting suspicious activity early. It’s not just noticing an alert. It’s confirming whether there’s an actual compromise. The faster you spot an attack, the lower the potential damage.
Key activities include:
- Collect and analyze logs from endpoints, servers, and cloud environments.
- Use Security Information and Event Management (SIEM) systems to correlate events.
- Determine the scope and severity of the incident.
- Prioritize which threats need immediate action.
3. Protect
Containment, or “protect,” is about limiting damage before it spreads. The goal is to stop the incident from escalating while preserving evidence for investigation.
Key activities include:
- Isolating affected devices or networks.
- Revoking compromised credentials.
- Segmenting systems to prevent lateral movement.
- Applying temporary controls to block further intrusion.
4. Detect
Detection ensures you catch new threats quickly and understand attacker behavior. It is an ongoing process as attackers often attempt to stay under the radar.
Key activities include:
- Monitoring for anomalies in user behavior, network traffic, and system logs.
- Using threat intelligence feeds to identify indicators of compromise.
- Automating alerts to reduce manual delays.
- Continuously testing monitoring tools to ensure accuracy.
5. Respond
The response phase covers both action and cleanup. Once an incident is confirmed, teams must act to neutralize threats and restore operations safely. It’s the “do, fix, and protect” phase rolled into one.
Key activities include:
- Removing malware and closing exploited vulnerabilities.
- Applying patches and updating security controls.
- Restoring systems from verified clean backups.
- Monitoring for signs of reinfection.
- Communicating internally and externally as per your plan.
6. Recover
Recovery is more than turning systems back on; it’s learning from the incident to prevent future breaches. Skipping this step guarantees repetition.
Key activities include:
- Teams review what went right and what went wrong.
- Detection gaps and delayed responses are analyzed.
- Incident response plans and playbooks are updated.
- Lessons are shared across teams to improve readiness.
You may also like: Indicators of Compromise Explained: How to Detect and Prevent Cyber Attacks
What Cybersecurity Incident Response Looks Like in Practice?

Below are the case studies that show how preparedness and transparency help to prevent damage.
1. Equifax Data Breach
Few breaches show the cost of poor preparation like this one.
On September 7, 2017, Equifax announced that attackers stole personal information from over 140 million consumers. The data included Social Security numbers, driver’s license numbers, email addresses, and credit card information. The scale of the breach shocked the public and regulators.
Attackers exploited their vulnerabilities, such as governance gaps, unclear accountability, and insufficient monitoring, to perform this breach.
Equifax’s public response faced strong criticism, too. CEO Richard Smith and several executives resigned. The company faced lawsuits, government investigations, and regulatory pressure. Equifax eventually made changes to strengthen its security posture and governance framework.
Key Lessons: Proactive preparation, continuous monitoring, and clear accountability are essential. Neglecting them can turn a breach into a catastrophic, multi-million-dollar crisis.
2. Norsk Hydro – How Transparency Minimized the Damage
Norsk Hydro (one of the world’s largest aluminum producers operating in more than 40 countries) experienced a major ransomware attack in March 2019.
Hackers used LockerGoga ransomware to lock files on thousands of servers and PCs. The attack disrupted global operations and cost the company tens of millions.
The attack began with a normal-looking email. An employee opened a malicious attachment from what appeared to be a trusted customer. That single action gave attackers access.
Leadership made three immediate decisions. They refused to pay the ransom. They brought in external incident response experts. They communicated openly about the breach.
Executives held daily press briefings. They hosted webcasts to update employees and the public. They posted regular updates while working with a specialized cybersecurity team to contain the attack. Their transparent response limited damage and built public trust during a global ransomware attack (CSO Online, 2019).
Key lesson: Tested backup and recovery capabilities allow organizations to recover. Transparent communication reduces uncertainty and builds trust during a major security event.
The Role and Importance of Cybersecurity Incident Response Tools

Modern cybersecurity teams use a combination of tools to respond effectively. Each tool supports a specific stage of the response process and improves speed and visibility.
1. Security Information and Event Management (SIEM)
Platforms such asSplunk and IBM QRadarprovide centralized visibility. They collect logs from servers, endpoints, networks, and cloud systems. They correlate events and identify suspicious patterns. They also generate dashboards and reports to support compliance and tracking.
2. Endpoint Detection and Response (EDR)
Tools such as CrowdStrike Falcon and SentinelOne monitor endpoint behavior. They detect abnormal activity and allow teams to isolate compromised devices remotely. They also collect forensic data for investigation and future improvement.
3. Security Orchestration, Automation, and Response (SOAR)
Platforms, including Palo Alto Cortex XSOAR and IBM Resilient, automate repetitive tasks. They disable accounts, quarantine emails, and create tickets automatically. Automation reduces response time and limits human error.
Forensic tools such as EnCase and FTK preserve evidence and analyze attack methods. Teams use them to capture disk images, analyze memory, and document compromised systems. This process helps determine root cause and supports legal or regulatory requirements.
Threat intelligence platforms such as Recorded Future and Anomali enrich alerts with attacker context. They provide infrastructure reputation data and known indicators of compromise. This information helps teams prioritize high-risk alerts and reduce false positives.
Who Do You Need for Your Effective Cybersecurity Incident Response?

Your incident response plan must include:
- Technical Team: They detect threats, analyze attacks, and defend systems in real time.
- Incident Response Coordinator: They manage the team, track progress, and ensure teams execute response steps efficiently.
- Executive Sponsor: They provide leadership oversight, align response with business priorities, and ensure resources are available.
- Legal Counsel & Outside Experts: They advise on compliance, regulatory risk, and specialized technical challenges.
- Media Relations Coordinator: They handle communication to the public, employees, and stakeholders, maintaining transparency and trust.
- Forensic Analyst: They investigate the root cause, preserve evidence, and guide future prevention measures.
5 Common Mistakes that Turn Cybersecurity Incidents into Crises

A cybersecurity incident does not become a crisis overnight. It escalates when preparation, clarity, and execution fall short at critical moments. Below are 5 such common mistakes that you should avoid:
- Assuming a documented policy equals readiness – Having a plan on paper does not guarantee the team can execute it under pressure.
- Unclear role ownership – Delays decision-making during critical moments. It slows detection, containment, and response.
- Untested or unreliable backups – Failures during recovery can prolong downtime and data loss.
- Outdated or incomplete playbooks – Lead to confusion and inconsistent actions when incidents occur.
- Poor communication strategies – Ineffective internal and external communication erodes trust and worsens reputational damage.
How AI is Transforming Cybersecurity Incident Response

Attackers are increasingly automating their attacks. So defenders are turning to artificial intelligence and machine learning to stay one step ahead.
In 2025 and 2026, organizations integrate AI-driven tools directly into incident detection and response workflows.
SentinelOne Singularity uses AI to detect, analyze, and respond without human delay. Its behavioral models identify ransomware and zero-day attacks in real time. The platform can remediate threats automatically.
Darktrace uses machine learning to establish a baseline of normal activity. It monitors networks, cloud workloads, and email systems. It then flags anomalies that signal a breach. This behavioral analysis helps detect advanced threats that bypass signature-based defenses.
AI has a measurable impact. Organizations that adopt these tools detect threats faster. They reduce response time and false positives. They automate routine containment tasks. This shift allows analysts to focus on strategy and decision-making instead of repetitive triage.
You may also like: 10 Best Important Tips and Ways to Improve Cybersecurity
Conclusion
Breaches are no longer rare events. They are operational realities. What separates resilient organizations from failed ones is cybersecurity incident response readiness. A structured lifecycle, trained teams, tested backups, and intelligent automation reduce damage when prevention fails. If your organization has not tested its incident response plan in the last 12 months, now is the time.
Start by reviewing your playbooks, running a tabletop exercise, and measuring your MTTD and MTTR. With the right response plan, challenges remain under control.
FAQ’s
1. How much does a cybersecurity incident response plan cost?
Costs vary by size and complexity, but even basic planning is far cheaper than recovering from a major breach.
2. Is incident response required for regulatory compliance?
Yes. Many regulations require documented procedures for detecting, reporting, and responding to security incidents.
3. Can small businesses implement incident response without a large IT team?
Yes. Even a simple, clearly documented plan with defined roles can significantly reduce damage during an incident.
4. Should companies outsource incident response?
Yes. Outsourcing incident response can help companies access specialized expertise, 24/7 monitoring, and advanced threat detection that may be difficult to manage internally. It ensures faster, more effective responses during attacks while reducing the burden on internal teams.
5. How often should you update incident response contacts and escalation lists?
Update them at least once every quarter to keep contact details and responsibilities accurate.






