In today’s digital world, it’s super important to keep your network safe from cyber threats. These threats are always changing and can cause big problems for businesses and regular people. That’s where network firewalls come in—they’re like special bodyguards for your network. But what are they and how do they keep your network safe? Let’s find out in this easy-to-understand guide about these important security gadgets.
Understanding Networker Firewall
Fundamental Definition and Core Functionality
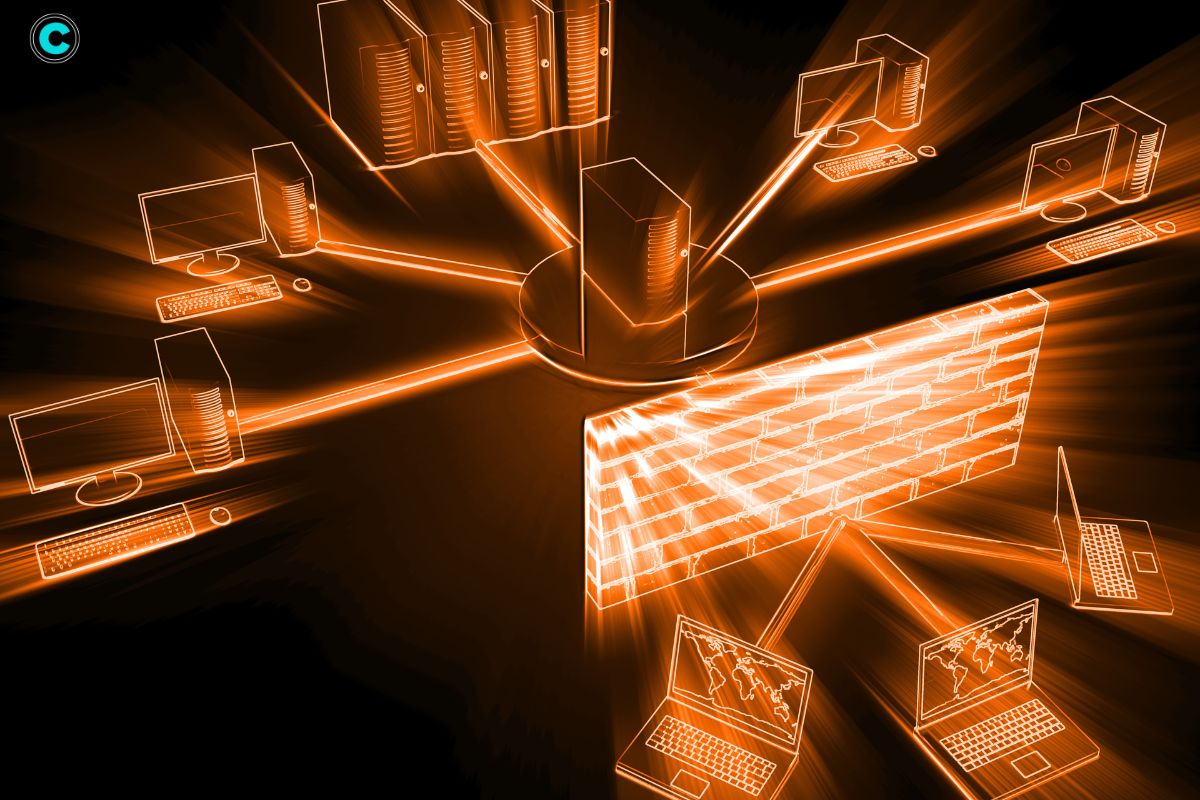
A firewall acts as a sentinel, monitoring and regulating the traffic that flows into and out of your network. It uses a set of predefined rules to filter this traffic, blocking harmful entities like viruses and unauthorized access attempts while allowing legitimate communications to pass through. Essentially, it serves as a barrier between your secure internal network and potentially dangerous external networks, such as the Internet.
Comprehensive Features of Networker Firewall
1. Intrusion Detection and Prevention Systems (IDPS)
Network firewalls often include IDPS, which monitors network traffic for malicious activities and policy violations. The system can automatically take action to prevent intrusions, such as blocking offending IP addresses or alerting administrators.
2. Deep Packet Inspection (DPI)
DPI allows the firewall to analyze the data within packets, not just their headers. This thorough inspection helps in identifying and blocking sophisticated threats that might slip past traditional firewalls.
3. Application Awareness and Control
With application awareness, network firewalls can identify and manage applications running on the network. This feature helps ensure that only authorized applications can access network resources, reducing the risk of attacks from malicious or unauthorized software.
4. Advanced Threat Protection (ATP)
ATP involves multiple layers of security measures designed to detect, analyze, and mitigate threats. This includes real-time threat intelligence, behavior analysis, and automatic response mechanisms.
5. SSL/TLS Inspection
Network firewalls can decrypt SSL/TLS traffic, inspect it for threats, and then re-encrypt it before forwarding it to its destination. This capability is crucial as more web traffic is encrypted, potentially hiding malicious content.
6. Sandboxing
Sandboxing isolates suspicious files and programs in a secure environment where they can be analyzed without posing a risk to the network. If the sandboxing process detects malicious behavior, the threat is neutralized before it can cause harm.
Benefits of Implementing Network Firewalls
1. Elevated Security Measures
Network firewalls provide multiple layers of security, significantly enhancing your network’s ability to resist cyber threats. They offer comprehensive protection against a wide range of attacks, from simple malware to complex, multi-vector threats.
2. Enhanced Network Performance and Efficiency
By managing and filtering traffic effectively, network firewalls help maintain optimal network performance. They prevent bandwidth hogging by unauthorized applications and prioritize critical business traffic.
3. Regulatory Compliance Adherence
Many industries are subject to stringent regulatory requirements regarding data protection. Network firewalls help organizations comply with these regulations by providing detailed logs and robust security measures that protect sensitive data.
4. Long-Term Cost Efficiency
While investing in a networker firewall involves an upfront cost, it can save significant expenses in the long run by preventing data breaches, reducing downtime, and avoiding regulatory fines.
Operational Mechanism of Network Firewalls
1. Continuous Traffic Monitoring
Network firewalls continuously monitor all incoming and outgoing traffic for signs of suspicious activity. This real-time monitoring helps in the early detection and mitigation of potential threats.
2. Sophisticated Rule-Based Filtering
These firewalls use a set of rules to filter network traffic. The rules can be based on various criteria, including IP addresses, port numbers, protocols, and even specific content within the packets. This granular control allows for highly customized security policies.
3. Integration of Virtual Private Network (VPN) Support
Many network firewalls come with built-in VPN support, allowing secure remote access to the network. VPNs encrypt data transmissions, making it difficult for unauthorized parties to intercept and read sensitive information.
Step-by-Step Guide to Setting Up a Networker Firewall
Preliminary Considerations Before Installation
Before installing a networker firewall, it’s essential to understand your network’s specific needs. Assess factors like network size, types of devices, typical traffic patterns, and security requirements.
Detailed Installation Procedure
- Choose the Right Firewall: Select a firewall model that meets your network’s demands.
- Connect the Firewall: Physically connect the firewall to your network infrastructure.
- Configure Initial Settings: Set up basic configurations, such as IP addresses, administrative access, and network interfaces.
Best Practices for Configuration
- Define Security Policies: Establish clear rules for traffic filtering based on your security needs.
- Enable Logging and Alerts: Set up logging to track security events and configure alerts for critical incidents.
- Regular Updates: Ensure that the firewall’s firmware and security definitions are kept up-to-date to protect against new threats.
Optimal Firewall Management Techniques
1. Ensuring Regular Updates and Patching
Regularly updating your firewall’s software and firmware is crucial for protecting against the latest threats. Set up a schedule for routine updates and patching.
2. Effective Monitoring and Logging Practices

Consistent monitoring and logging are essential for identifying and responding to security incidents. Review logs regularly to detect unusual activities and refine your security policies.
3. Policy Creation and Enforcement
Develop comprehensive security policies that cover all aspects of your network’s operations. Ensure these policies are consistently enforced across the network to maintain a high level of security.
Addressing Common Challenges
1. Minimizing False Positives
False positives can be a significant issue, as they may block legitimate traffic and disrupt business operations. Fine-tune your firewall settings to reduce false positives and ensure a balance between security and usability.
2. Simplifying Firewall Complexity Management
Managing complex firewall configurations can be challenging, especially for large networks. Utilize centralized management tools to simplify configuration, monitoring, and policy enforcement across multiple firewalls.
3. Balancing Security Requirements with Network Performance
While it’s crucial to maintain robust security, it’s also important to ensure that the firewall doesn’t impede network performance. Optimize firewall settings to achieve a balance between strong security measures and efficient network performance.
Selecting the Appropriate Networker Firewall
Key Factors for Consideration
1. Network Scale and Complexity
Choose a firewall that can handle the volume and complexity of your network traffic. Consider the number of users, devices, and the types of applications running on your network.
2. Budget Constraints
Evaluate the total cost of ownership, including purchase, installation, maintenance, and potential upgrades. Balance your budget with the need for comprehensive security features.
3. Specific Security Requirements
Assess your network’s unique security needs, such as protection against specific types of threats or compliance with industry regulations. Choose a firewall that addresses these requirements effectively.
4. Leading Networker Firewall Brands
- Cisco: Known for its robust security features and reliability.
- Fortinet: Offers high-performance firewalls with integrated threat intelligence.
- Palo Alto Networks: Provides advanced security solutions with deep visibility and control.
- Checkpoint: Renowned for its innovative security technologies and comprehensive protection.
Case Studies: Practical Applications of Network Firewalls
1. Small Business Implementation Scenario
A small business implemented a networker firewall to protect its customer data and prevent cyberattacks. The firewall provided enhanced security measures, allowing the business to maintain customer trust and comply with industry regulations.
2. Enterprise-Level Deployment Example
A large enterprise deployed a networker firewall to secure its extensive network infrastructure. The firewall’s advanced features enabled the enterprise to protect against sophisticated threats, ensure regulatory compliance, and maintain efficient network operations.
Emerging Trends in Network Security
1. AI and Machine Learning Integration
Future firewalls will increasingly leverage artificial intelligence and machine learning to detect and respond to threats more effectively. These technologies can analyze vast amounts of data to identify patterns and anomalies that indicate potential attacks.
2. Evolution of Cloud-Based Firewalls

As more organizations move to cloud environments, cloud-based firewalls are becoming more popular. They offer scalability, flexibility, and the ability to protect cloud resources from various threats.
3. Enhancing IoT Security Measures
The proliferation of Internet of Things (IoT) devices presents new security challenges. Specialized firewalls designed to secure IoT devices and their communications will be crucial in protecting against threats targeting these devices.
FAQs
1. What is the main purpose of a networker firewall?
A networker firewall’s primary purpose is to monitor and filter incoming and outgoing network traffic to protect against malicious activities.
2. How often should I update my firewall?
It’s recommended to update your firewall’s software and firmware regularly, typically as soon as updates are released.
3. Can a networker firewall improve my network’s performance?
Yes, by efficiently managing traffic and mitigating threats, a networker firewall can enhance your network’s performance.
4. What should I consider when choosing a networker firewall?
Consider factors like your network’s size, budget, and specific security needs when selecting a firewall.
5. Are cloud-based firewalls as effective as traditional ones?
Yes, cloud-based firewalls offer comparable security to traditional firewalls, with added benefits like scalability and flexibility.
Conclusion
Network firewalls are indispensable tools for modern network security. By understanding their features, benefits, and implementation, you can effectively protect your network from a wide array of threats. Staying informed about the latest trends and best practices will ensure your network remains secure in an ever-evolving digital landscape.






