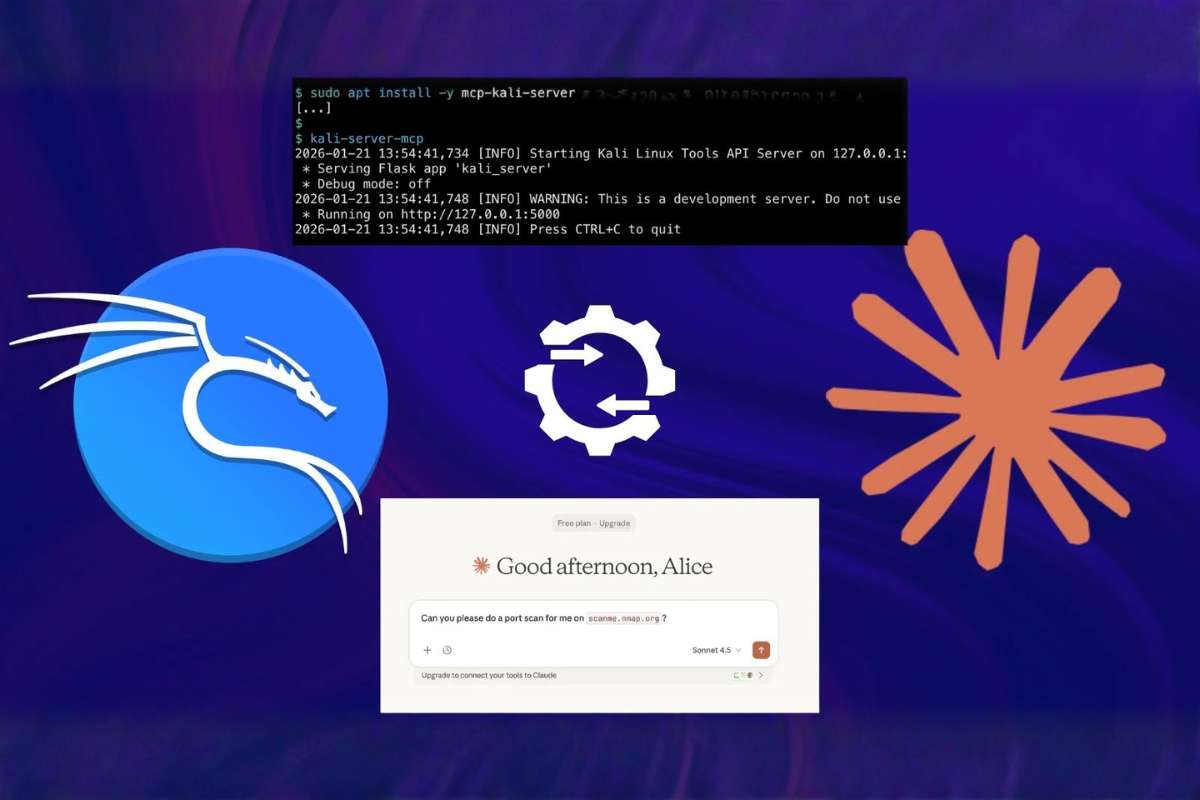
Kali Linux has introduced a native artificial intelligence-assisted penetration testing workflow that enables AI-Driven Penetration Testing, allowing security professionals to execute cybersecurity tasks using natural language commands. The new system connects Anthropic Claude artificial intelligence with a live Kali Linux environment, enabling automated execution of security testing tools through conversational input.
AI Integration Changes Traditional Security Testing Methods
The newly introduced workflow moves beyond traditional command line interaction that has long defined penetration testing practices and advances AI-Driven Penetration Testing methods. Instead of manually typing complex commands, cybersecurity professionals can now describe tasks in plain language. The artificial intelligence system interprets the request, selects suitable tools, executes commands, and presents structured results.
For example, a tester can request a port scan and file verification through a single prompt. The artificial intelligence engine then plans the required steps and performs them directly within the Kali Linux system without manual intervention.
This workflow operates through three connected layers. The user interface layer provides natural language interaction through Claude Desktop. The execution layer runs within a Kali Linux environment using a dedicated server bridge that connects security tools to artificial intelligence workflows. The intelligence layer processes prompts using the Claude Sonnet 4.5 model hosted in the cloud.
Together, these layers create a continuous operational cycle where prompts are interpreted, commands are executed, results are analyzed, and follow up actions are performed when required.
Model Context Protocol Enables Automated Tool Execution
The integration relies on the Model Context Protocol, an open framework designed to connect artificial intelligence systems with external software environments that support AI-Driven Penetration Testing. The protocol allows artificial intelligence models to maintain operational context while interacting with multiple cybersecurity tools during a testing session.
When a request is submitted, the system determines which security tool is needed and sends structured instructions to the Kali execution server. The server runs the command and returns organized output to the artificial intelligence model. The model then interprets findings and may initiate additional commands to complete the requested task.
Supported tools include widely used penetration testing utilities such as Nmap for network scanning, Gobuster for directory discovery, Nikto for web server analysis, Metasploit for exploitation tasks, SQLMap for database testing, and credential auditing tools such as Hydra and John the Ripper.
Testing demonstrations showed that prompts requesting network analysis triggered automatic verification of tool availability, followed by execution and reporting without manual command entry. System logs confirmed live execution and structured communication between artificial intelligence and security tools.
Cybersecurity researchers note that artificial intelligence-driven workflows introduce operational considerations related to access control and monitoring in AI-Driven Penetration Testing systems. Experts recommend limiting permissions, validating command inputs, and maintaining detailed execution records to ensure responsible deployment within testing environments.
The Kali Linux development team describes the integration as an evolving method rather than a replacement for established workflows. Organizations using artificial intelligence testing are encouraged to evaluate operational requirements before routing commands through cloud-based intelligence systems.
The introduction marks a significant step in the adoption of artificial intelligence within offensive security practices. By combining reasoning capabilities with automated tool execution, AI-Driven Penetration Testing workflows are becoming more guided and accessible while maintaining technical depth. As adoption expands across cybersecurity environments, conversational artificial intelligence is expected to play an increasing role in vulnerability assessment and security analysis.